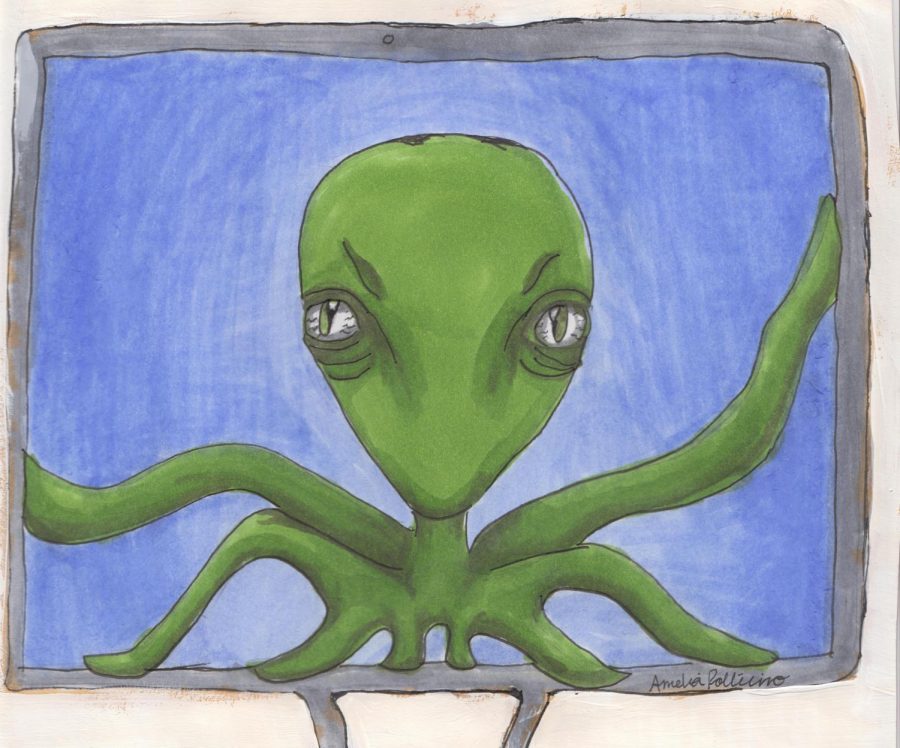
Virus Takeover
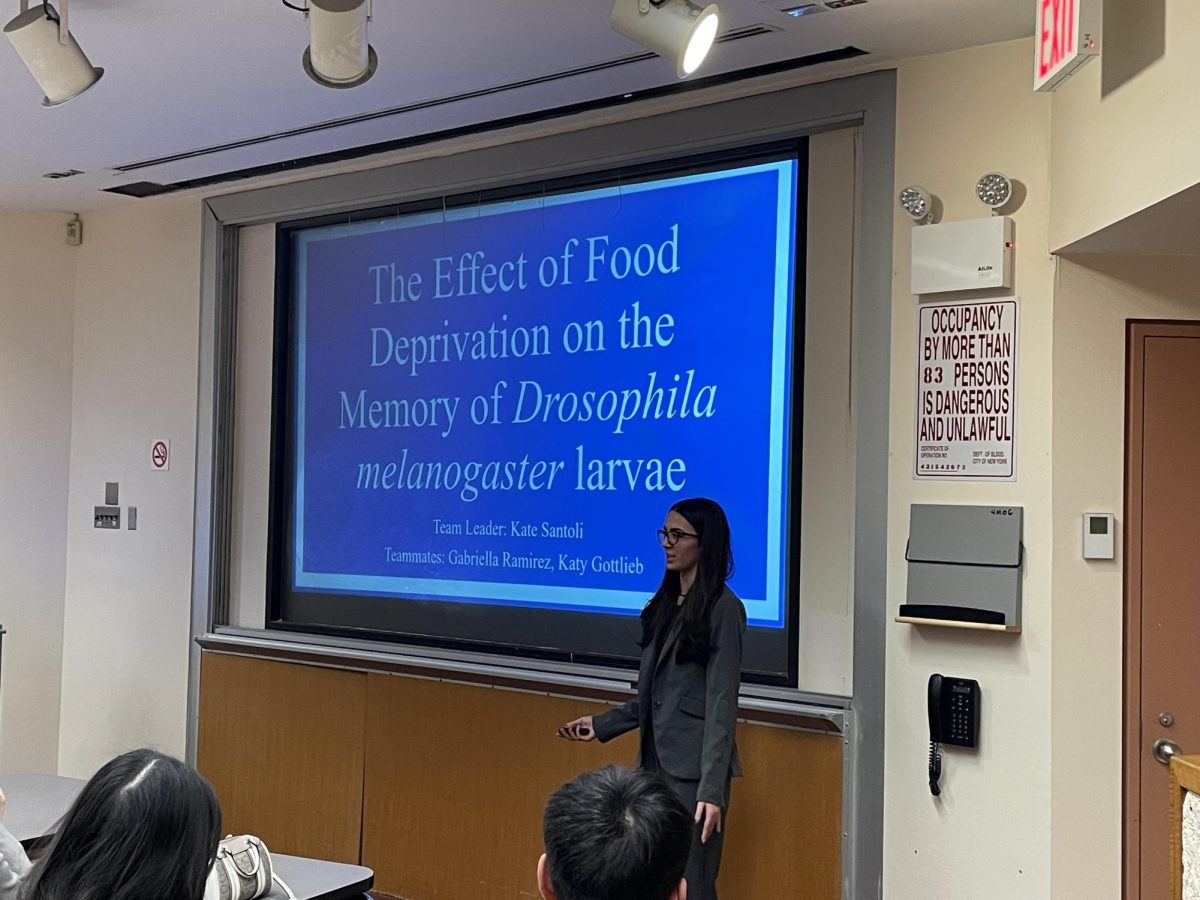
After returning from Martin Luther King weekend on Jan. 23, Principal Joe Rainis announced that a computer virus had infected all desktop computers district wide. The virus, which replicates and transmits via scam email, forced the district to permanently disable its email domain @lynbrook.k12.ny.us, and prohibited desktop computer use until the IT department was able to analyze the threat and completely scrub and restore every wired computer. This impaired technology-oriented classrooms: “It has impacted the day to day operation of LHS. I long for the days of using PowerPoint,” commented AP Psychology and U.S. History Teacher John Cornicello.
The virus, emotet malware, was initially created in 2014 in an attempt to infiltrate banking systems to steal identities and wipe out bank accounts. Since then, it has adapted and gravitated towards attacking less secure environments (such as school districts), to search for and extract sensitive personal and financial information.
The virus’s “worm-like” features allows it to rapidly multiply and spread, oftentimes in different forms, increasing its severity day by day. The United States Computer Emergency Readiness team describes emotet as being among the “most costly and destructive malware affecting state” and has revealed that emotet infections have cost the government up to $1 million per incident to repair.
The virus first breached Lynbrook’s network on Jan. 19 when a series of junk e-mails first appeared in staff’s online inboxes. It immobilized the district for nearly two weeks, until Jan. 31 when teachers and students were given the okay to use school desktops. However, even in the second week of February, many necessary applications, like InDesign, and Ladybug software, were still uninstalled, disabled, or functioning poorly on desktop computers.
Emotet attacked Lynbrook’s server through school email but quickly attempted to infiltrate the district’s accounting system and all of the private information contained in Powerschool. Fortunately, the IT department was able to determine that those systems had not been penetrated and swiftly disconnected both applications. Anyone within the district who had done online banking or who had logged into accounts from desktop PCs using credit card information (most notably Amazon.com) on any school desktop was vulnerable to compromising his/her passwords and account information, raising the concern of identity theft.
To the dismay of many teachers and students, until a complete solution was found, many teachers had resorted to more traditional teaching styles, instructing students to take handwritten or typed notes rather than projecting PowerPoints, a feature that was also crippled by the virus. English Teacher Carla Gentile jokes that this adapted form of teaching was almost like visiting what seems like the distant time before technology:“I’ve always wanted to know what it’s like to live on the prairie, and now I feel like I do. I can now say I don’t want to live there.”
Fortunately, when designing the Lynbrook server, the IT department had assembled the network with levels of redundancy and separateness, allowing them to appropriately rectify the issue at an increased rate. The isolated servers had limited the virus from spreading as far as it potentially could have, significantly decreasing its expected damage. Still, almost all desktops district wide were affected by the malware and, as Rainis explained, “the IT department had to go to each building and scrub each machine,” a process that “took some time.”
Lynbrook is currently in its remediation stage of recovery, in which the complete shift to Office 365 and its respective @lynbrookschools.org email domain, which was scheduled to happen this summer, is being expedited to completely abandon the old, compromised system. From now on, students and teaches will only have access to their @lynbrookschools.org emails. While this is more of an inconvenience than a problem for most of the student body, seniors who used @lynbrook.k12.ny.us for their Common Application and other college contact information had to contact these organizations and colleges to make sure they did not miss any important information and to change their contact email. Even worse, teachers, some having been in the district for decades, have lost all their contacts that were saved in the old system, all their old emails (that may have had important information), and anything else accessible only through their old accounts. This pertains especially true for long time English Teacher and SGA Advisor Mary Kirby: “I have had my K12 email for almost 23 years. It sounds very silly, but I feel as though I lost a part of me. Unfortunately, I have used my email as a source to save information for many of the responsibilities that I have here in Lynbrook. Whether it was key information or contacts that were saved for an English class, the SGA, or the Lynbrook Teacher Center, I was not prepared to say goodbye to that email forever!”
Although the district’s IT department had planned to briefly open the @lynbrook,k12.ny.us server to allow teachers to access and transfer all important information contained within the system, unfortunately, that is no longer a possibility: “There has been a serious attempt on our behalf to try and get [the @lynbrook.k12.ny.us] server back, but there was serious damage done to that mail server… instead of trying to spend a lot of resources, time, and money to resuscitate a mail server that we were going to retire in less than 6 months, we decided not to invest in that direction. So, @lynbrook.k12.ny.us is not going to come back,” explained I.T. coordinator Neil MacDermott
While it appears the malware issue has been completely resolved and viable solutions have been reached, concerns of the virus have not been entirely alleviated. As MacDermott explains, the emotet virus is something the IT department “anticipates is going to be a problem that is ongoing.” The department is currently consulting with experts in the field and are in the process of evaluating new technology, appliances, or software that may need to be purchased and installed on the district’s devices in order to help prevent emotet, or similar viruses, from breaching the network in the future. Until then, in hopes of preventing the virus from spreading, the IT department is prohibiting– as they did during the peak of the virus– usage of any USB flash drives in all school owned devices.

I am a member of the Class of 2020. In my free time, I write articles for Horizon. I am the editor-in-chief for the print edition for 2019-2020.